Compliance standards and guidelines continue to gain traction and are being implemented in many industries as well as across local and national government agencies. While some standards are optional, the majority are required and often levy hefty fines for noncompliance. Popular opinion is that only companies within regulated industries need to worry about cybersecurity, believing that data protection is only a requirement for regulatory compliance.
However, any organization that receives, stores, or handles consumer or sensitive business data needs to protect that information — it’s always at risk. Hackers never stop looking for the weakest link in a network, and employees can pose threats through negligence or bad intention.
Click Here To Discover The Multi-Million Dollar Compliance Goldmine That MSPs Are Sitting On
What is regulatory compliance?
Regulatory compliance is a set of rules that organizations must follow to protect sensitive information and human safety. This means following external legal mandates set forth by the state, federal, or international government.
Here are our top four tips for cybersecurity regulatory compliance:
1. Identify Which Requirements May Apply.
First, determine which regulations or laws you and your customers must follow. To start, data breach notification regulations exist in every state in the United States, requiring you to tell customers if their personal information is compromised.
For example, if your business deals with the financial information of a New York resident, you would be subject to the New York Department of Financial Services (NYDFS) Cybersecurity Regulation’s set of standards.
Furthermore, the California Consumer Privacy Act and the NYDFS Cybersecurity Regulation impose restrictions that may apply to your firm based in any state if you deal with data covered by these laws.
2. Implement Policies, Procedures, And Process Controls.

It’s not only about technology when it comes to cybersecurity regulatory compliance. It’s also critical for both compliance and safety to have risk-mitigation policies and processes in place. There’s no technical precaution in the world that can prohibit a committed employee from downloading malware to company systems or visiting unsafe websites.
3. Conduct Regular Audits And Technical Reviews.
It’s essential to perform regular audits (or technical reviews) of your own IT security and privacy programs, systems, and software to be sure they are providing the protection you think they are. Although, there’s still no guarantee against a data breach even if you are doing all the right things correctly. That’s why it’s essential you maintain ongoing documentation of your own compliance efforts to protect yourself by showing “due care” and side-stepping accusations of negligence.
4. Invest In The Right Tool.
Make your life simpler by investing in the right tool. Compliance Manager GRC, a Kaseya company, for example, gives you the power to reduce IT risk by ensuring compliance with government or industry standards. It also encompasses custom IT requirements included in any business contract, any insurance policy, or your own IT security policies and procedures. It automates data gathering, issue management, and all the documentation required to prove due care to any internal or external auditor.
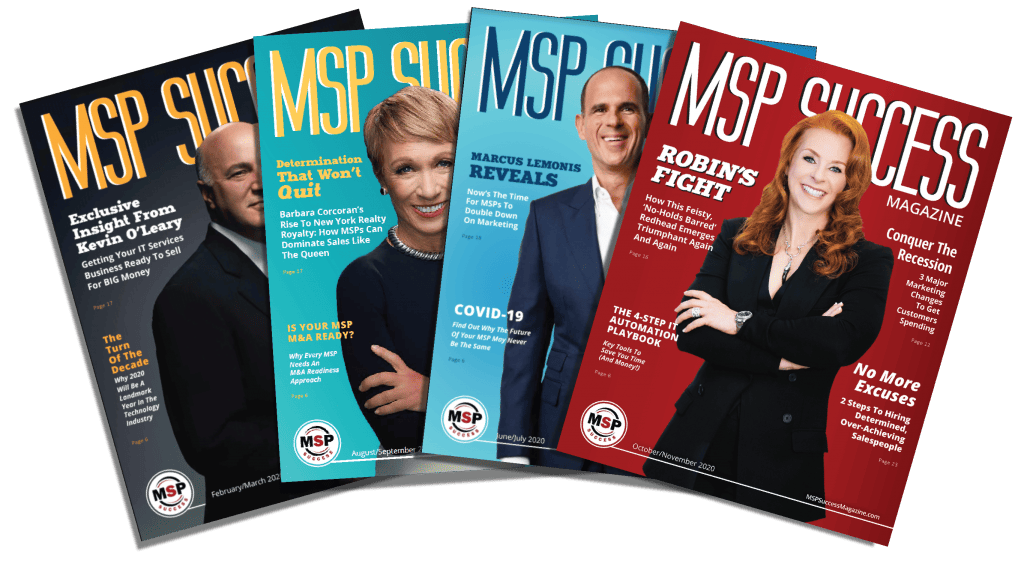
Are you an MSP or IT services CEO, who wants help with a PROVEN plan to successfully grow your business? Click Below To Take The First Step